Guest Lecture: Let's Make Cybersecurity Real!
This is an archived post. Originally published: 18/11/2023
It's been very nearly an entire year since I gave my last guest lecture on the future of machine learning to Data Analytics students at NHL Stenden back in February. Since then, I've moved on from my position as Head of Software Engineering at BreachLock and taken the leap into entrepreneurship. I'm loving my new role as CTO and Co-Founder of Noon at Work, and relishing the learning and growth I've enjoyed since I joined the awesome folks at Builders in building out their newest venture, but I'd be lying if I told you I don't sometimes get nostalgic for the times when cybersecurity was my day-to-day.
That's why it was so refreshing and exciting to have the opportunity to deliver my first guest lecture at NHL Stenden's Emmen campus, focusing on making cybersecurity less of a mystery to students on the International Business program!
My aim was to take the very nebulous and spooky concept of "being hacked" and make it a real, concrete thing that International Business students brand new to cybersecurity could better conceptualise and understand. What does an incident actually look like? How do we tread the line between cyber paranoia (which can actually make system security much worse) and recklessness that puts customer data and company assets in danger?
What does a padlock do? Who does it keep out?

We used a set of pin-tumbler lockpicks and some transparent acrylic practice locks to answer an important question: what do security measures like locks actually achieve?
We kicked off with a thought experiment and practical demonstration. We asked ourselves the question:
What does a padlock do, and who does it keep out?
The obvious answer is "it prevents thieves from gaining entry" but this is an oversimplification. This practice lock (and many other real padlocks out there on the market) can be "raked" open with a tool costing less than $1 in five seconds flat. Add a pair of bolt cutters into the equation, and that time may well come down even further. A number of the students attending the session were able to open this practice lock with only a 2-minute tutorial, despite never having seen or handled lockpicks before (they were obviously warned to only use their new-found understanding of locks only for good and never evil).
The actual answer is more nuanced. A padlock like this keeps out honest people and opportunists—dishonest folks looking for an easy target. Using a padlock like this to secure your garden shed where you keep your rusty old lawnmower? Great! Use it to secure your jewelry store with $100,000 of jewelry and precious metals on-site? Not such a good idea.
This led us to the first of two lifelines business folks can use to get a handle on their cybersecurity posture: what does your *threat model* look like?
Threat modelling is the process of identifying threats to your system and defining measures to counteract them. It's a great antidote to both carelessness and paranoia!
Is your web development agency maintaining a WordPress site for a local furniture store? If so, keeping your WordPress installation (and plugins!) patched and up-to-date and responding in a timely fashion to newly-disclosed vulnerabilities is reasonable. You probably don't need a dedicated cyber incident response team on-call 24/7, or a comprehensive network intrusion detection setup.
By contrast, has your consultancy been contracted by the government to manage and maintain critical network infrastructure that keeps the electricity grid online? Different threat model altogether!
While businesspeople may not be engaging in cyber threat modelling personally on a day-to-day basis, they are often the ones signing off on cybersecurity budgets. A little knowledge on what threat modelling looks like can help enormously in keeping communication with operations smooth and productive (especially during incident retrospectives).
What does a cybersecurity incident look like?
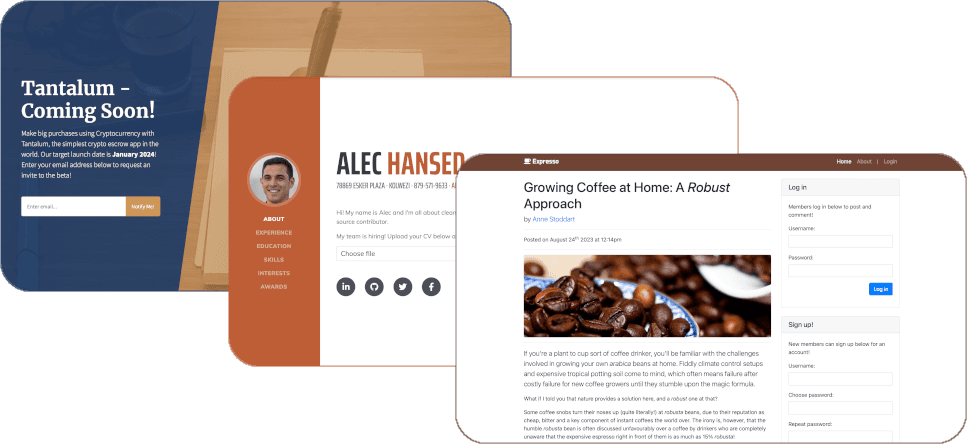
The 3 hackable websites hosted for the session.
Next, the class split into 3 teams, each of whom launched a simple cyberattack on one of 3 vulnerable websites hosted specifically for the session (again, students were warned never to use what we learned in the session against any real website).
The aim was to put the students in the attacker's seat for a moment—to help turn the threat of a cybersecurity incident into more of a known quantity that can be anticipated and planned for.
Briefly:
Team 1 attacked a hiring manager's website allowing unrestricted file uploads, enabling remote code execution with a web shell. Their goal: deface the homepage.
Team 2 attacked a crypto escrow landing page using HTML injection to grab the admin's credentials via a fake session dialog.
Team 3 exploited a password exposure vulnerability on a blog to steal the admin's credentials and log in as them.
All 3 teams, despite being new to offensive cybersecurity, successfully executed the attacks using prepared payloads.
We concluded with our second cybersecurity posture lifeline: what part of the attack surface of each site did we exploit?
First order of business when assessing cybersecurity risk is to understand your organisation's cyber attack surface—all the different ways someone can attack your systems.
Tying Things to the Real World
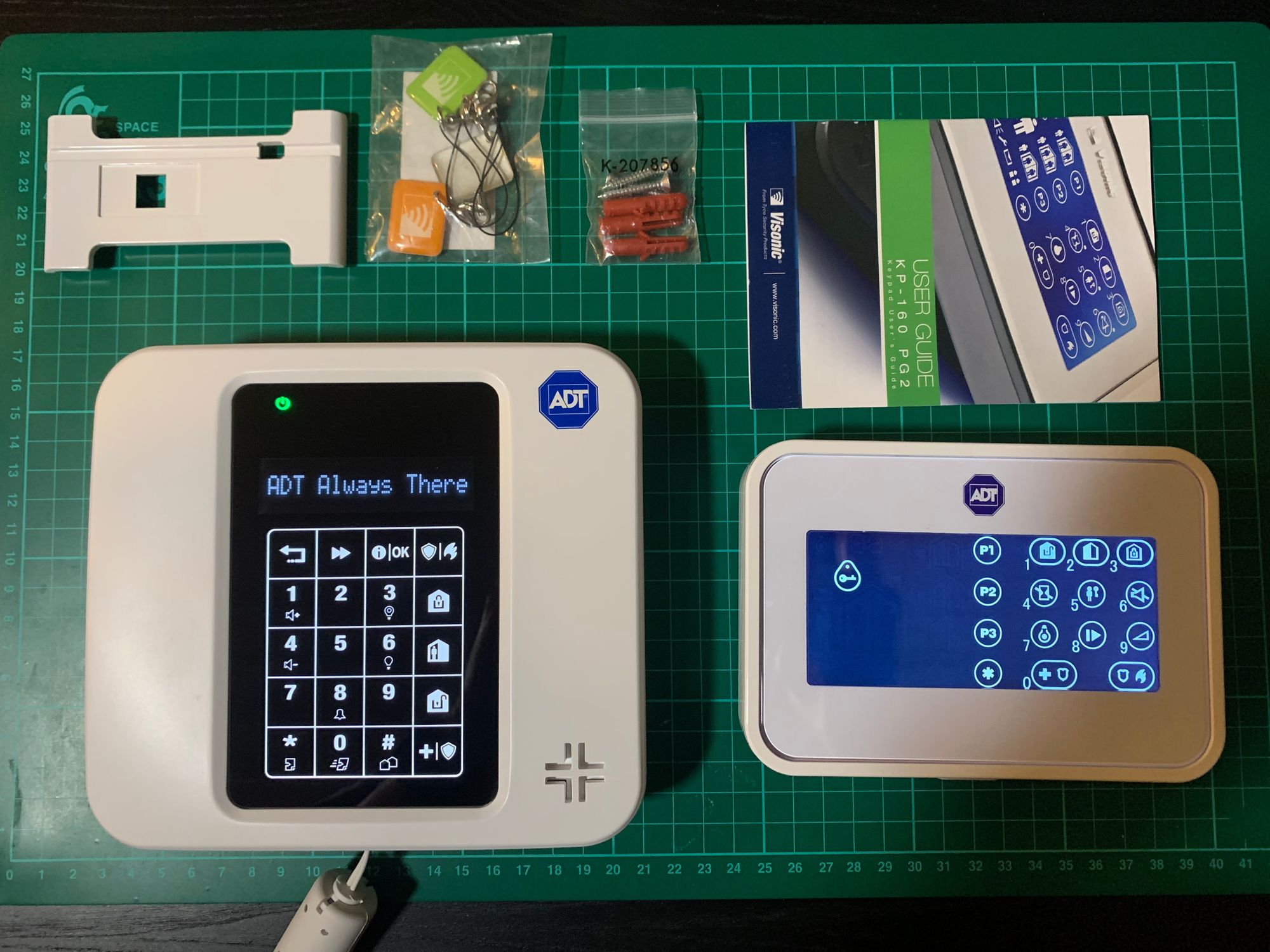
The burglar alarm system we used during the practical session.
To close, we ran a key cloning attack against an ADT-branded Visonic PowerMaster PM-360R burglar alarm using RFID fobs (details omitted—see my PhD thesis when it's done!).
We reflected on whether this system would be sufficient given different threat models and attack surfaces.
Wrapping Up
I'm set to deliver several more guest lectures at NHL Stenden before the end of the year. The campus facilities are excellent and the students are deeply engaged.
As ever, the lecture materials are open-source:
Password exposure: https://github.com/lambdacasserole/password-exposure-exercise
HTML injection: https://github.com/lambdacasserole/html-injection-exercise
Unrestricted file upload: https://github.com/lambdacasserole/unrestricted-file-upload-exercise
The slides and worksheets for the session team 1, team 2, team 3 are available on my website.

